[3 min. read]
by Allan Jacks, vCISO
As my roles changed, one of the most challenging times was when I had to complete an internal
audit in my role as an Engineer. I had to learn what controls were and about collecting evidence.
No longer was it acceptable to just have a task list with monthly to-dos checked off. The
document had to have the person’s name detailing who completed it, the time and date of
completion, and any comments that would reference any action taken or not taken. The internal
auditor then gave me a rundown on some things that would help me including an understanding
of what a control is.
What is a Control?
A control is a set of rules or procedures implemented within a company to ensure the integrity of
data and processes that a system supports. Common controls are things such as backup controls,
separation of duty controls, and physical security controls.
As you read through articles or security websites, you may see references to CIS Controls.
The Center for Internet Security (CIS) is a “community-driven nonprofit, responsible for the CIS
Controls and CIS Benchmarks, globally recognized best practices for securing IT systems and
data. We lead a global community of IT professionals to continuously evolve these standards and
provide products and services to proactively safeguard against emerging threats.”
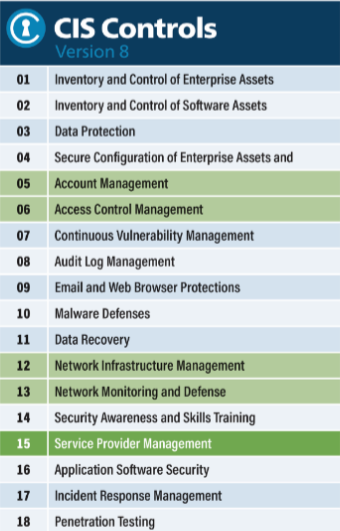
What are the 18 CIS Controls?
In May 2021 CIS launched the latest version of the CIS controls v 8.0 which took the list of 20 controls to 18.
These controls address areas of IT risk and form the foundation for a strong cybersecurity
program. The CIS Controls are an international-level collection of the best security practices to
implement.
Each item is a starting point that defines controls that guide security improvement within your organization. CIS Control 01 Inventory and Control of Enterprise Assets states:
“Actively manage (inventory, track, and correct) all enterprise assets (end-user devices, including portable and mobile; network devices; non-computing/Internet of Things (IoT) devices; and servers) connected to the infrastructure physically, virtually, remotely, and those within cloud environments, to accurately know the totality of assets that need to be monitored and protected within the enterprise. This will also support identifying unauthorized and unmanaged assets to remove or remediate.”
If you don’t know what assets you have, how do you go about protecting them? It also allows you to know when you see an asset that is not on this list, that an action should be taken. You can have a policy and a supporting control that only authorized and approved devices are allowed on the network. For any device not listed in this inventory, a defined action needs to be taken.
What is the Purpose of Controls?
CIS is focused on protecting and tracking high-risk areas of the business by using controls. They should be considered a good starting point for organizations to implement and allow their focus to initially be the protection of the business’s high-value assets.
The CIS Controls are not a replacement for other existing frameworks such as NIST 800-53, NIST Cybersecurity Framework, or ISO 27000, but you will find many of the controls mapped to these frameworks. If the CIS controls are a company’s initial focus, this will allow the groundwork for further implementations of other frameworks. The controls comply with the most applicable laws and security safeguards.
CIS Control Groups
Not every business will have the means or budget to implement all the controls, so CIS developed three different implementation groups with recommendations for safeguards for each group.
Implementation Group 1
Has 56 safeguards and is focused on protecting IT assets and personnel for small to medium-sized businesses.
Implementation Group 2
Has 130 safeguards and typically has multiple departments and risks based on job functions.
Implementation Group 3
Has 153 safeguards, and the organization typically has sensitive information and regulatory and compliance requirements.
Need Help with Controls? Trust Morefield
The implementation of CIS Controls is a great starting point for organizations to implement especially if they don’t have Governance requirements to follow a specific framework. Implementing the controls will mature the organization’s cybersecurity maturity level and will assist in minimizing exposure and risk leading to Cyber-Attacks and threats.
At Morefield, we can assist in the implementation of these controls and provide recommendations and guidance for fulfilling the requirements of each control. Contact us today!
References: